It’s important to protect our privacy online by using free and open source software and by following healthy digital practices, but it’s equally important to guard ourselves against mass surveillance when we are offline.
The two most commonly used methods for mass surveillance in the physical world are surveillance video cameras and mobile telephony. Using video cameras, often accompanied by facial recognition software, or data gathered by mobile carriers that can track the movement of mobile phone users, government agencies and private companies invade our private lives and retain large amounts of sensitive personal data without our consent. The argument that you shouldn’t worry about mass surveillance as long as you have nothing to hide doesn’t hold water. We all have something to hide. If you disagree, consider making your credit card numbers public by posting them on social media.

According to Wikipedia, mass surveillance “is the single most indicative distinguishing trait of totalitarian regimes”. This is understandable, since a totalitarian regime is based on a unanimity of political opinion artificially achieved by the use of force, threats and terror. To control a population by force, you need to know what everyone is doing at all times, therefore, you need mass surveillance. However, today even western democracies who pretend to respect the civil rights and liberties of their citizens, use mass surveillance to an extent comparable to that in totalitarian regimes.
The threats associated with mass surveillance are much worse than a few decades ago because law enforcement officers can use mass surveillance techniques to arrest individuals who are wrongly identified as suspects by facial recognition systems. Because of the high number of false positives generated by these systems, you could end up in police custody and face interrogation, even if you are the most honest and peaceful person in the world.
For example, police forces in the UK used automated facial recognition systems to identify individuals and arrest suspects. In 2018, a report of ‘Big Brother Watch’, a British civil liberties organisation, found that these systems were up to 98% inaccurate. Also, in the US state of Maryland, police used facial recognition by comparing people’s faces to their driver’s license photos. This practice was criticized when it was used in Baltimore to arrest protesters after the death of a black man in police custody. In 2025, the New Orleans Police Department used what was called “the first known widespread effort by police in a major US city to use AI to identify people in live camera feeds for the purpose of making immediate arrests“. All this is done even if it’s well known that “individuals with very dark skin are hard to identify with high significance via facial recognition” and “individuals with very pale skin are the same,” as a software engineer states.

When you are in a public place, such as on a busy street, in an institution, a supermarket, an aeroport, etc., it’s enough to raise your eyes to see numerous surveillance cameras watching and recording every move you make. In addition, cell phone towers receive periodic signals from your phone, so that your location and movements are always known to your mobile carrier and to those with whom they share your data.

Ignoring these intrusions in our private lives or being complacent about them is not an option for people who care about privacy, love freedom and are used to thinking with their own heads.
An adequate fight against these threats must be waged in two ways:
- actively – by asserting the right to privacy as an essential civil right and pressuring policymakers to end mass surveillance, and
- passively – by legally obstructing mass surveillance, such as by wearing accessories that prevent facial recognition.
This article describes the passive methods, which are simple, discreet and legal ways to defend our privacy.
Different passive methods have been proposed to fight the type of surveillance described above. Please note that we are not discussing targeted surveillance, such as when you are followed by secret service agents who take pictures of you, etc. That is much more difficult to evade. We are discussing mass surveillance, which means surveillance in which an entire population is monitored by government or private corporations using standard devices and techniques that are much less sophisticated than those involved in targeted surveillance.
The best passive methods to fight mass surveillance are those that meet four conditions:
- they are effective
- they are easy to adopt
- they are affordable
- they don’t attract attention
We describe them below.
Mass surveillance based on video footage is frequently associated with automated facial recognition. Broadly speaking, there are four steps involved in automated facial recognition: face detection, alignment (to account for face position, image size, brightness, etc.), feature extraction and face matching against a database of faces. The algorithms used in facial recognition analyze certain distinctive face features, such as the contour of the eyes, nose, cheekbones and chin, with a focus on the area at the intersection of the eyes with the nose.
Some systems use visible light and 2D facial mapping, while more advanced systems use infrared (IR) light and 2D or 3D facial mapping. The main advantage of infrared light is that it’s invisible to the naked eye, it provides visibility even in low-light and nighttime conditions, and penetrates eyeglasses, even regular sunglasses with dark lenses.
Facial recognition has been already used as a form of biometric authentication for different platforms and devices: Android’s ‘Face Unlock’ introduced in version 4.0, Apple’s ‘Face ID’ introduced in iPhone X, Microsoft’s facial recognition login used in its Xbox 360 video game console as well as the ‘Windows Hello’ feature introduced in Windows 10. In fact, when anyone wants to test a method that is believed to obstruct facial recognition, one of the easiest methods is to try to unlock an iPhone with one’s face while wearing the respective glasses / hats / face masks, etc. Apple’s ‘Face ID’ uses a system that projects and reads more than 30,000 infrared dots to map a user’s face. This system is by far more advanced and accurate than the majority of facial recognition systems used with surveillance cameras installed in public places.
Covering the eyes with regular sunglesses is known to disrupt facial recognition that uses visible light, yet, as mentioned, cameras with infrared light can easily penetrate regular sunglasses, hence the need to create lenses that can reflect infrared light to such a degree that it makes facial recognition fail. The only sunglasses with infrared-blocking lenses that are known to defeat standard facial recognition systems and that deserve to be mentioned, are the reflectacles, which are too expensive, have a limited number of models and are not sold with prescription lenses (with infrared reflective capabilities), some protection glasses worn by welders such as this or this, which you could hardly wear outside a workshop because they are too dark and they have an industrial looking design, and the glasses manufactured by Zenni Optical, which are effective, affordable and the most good looking of all.
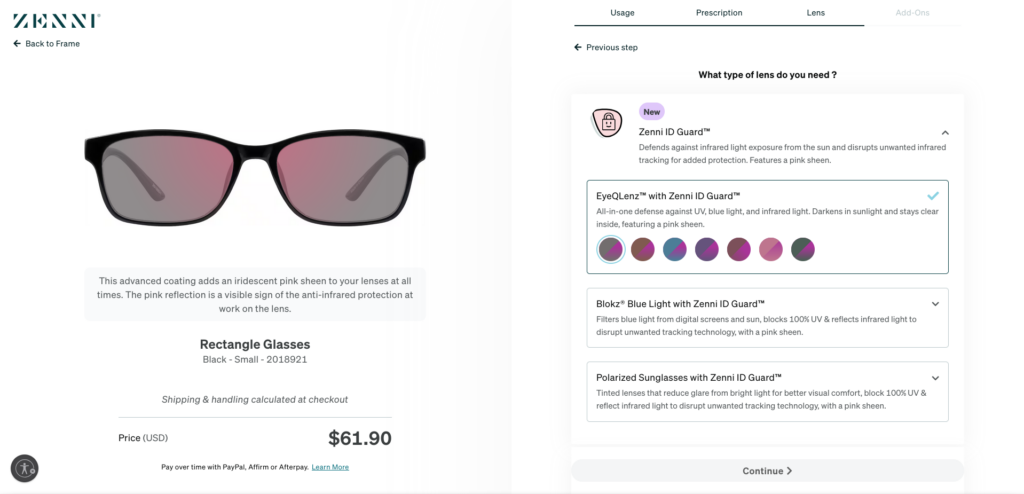
Zenni Optical offers in fact a special coating called Zenni ID Guard, which can be added to many types of their lenses, even to prescription lenses, which can be fitted into hundreds of different frame models. Zenni Optical’s glasses with infrared-blocking coating are known to block Apple’s ‘Face ID’, and they can also filter ultraviolet and blue light. Zenni ID Guard reflects up to 80% of near infrared light (700 nm – 780 nm) and infrared light (780 nm – 1050 nm), which can block IR light-based facial recognition systems.
When you visit the page that lists the frames compatible with lenses with infrared blocking coating, you can choose any frame model by clicking on its image, then you can choose a frame color, then, if you click ‘Select Lenses’ you can choose from a wide variety of prescription or non-prescription lenses, you can enter the prescription details, then you can choose to add the Zenni ID Guard feature, plus protection against ultraviolet and blue light, by clicking “EyeQLenz with Zenni ID Guard”:
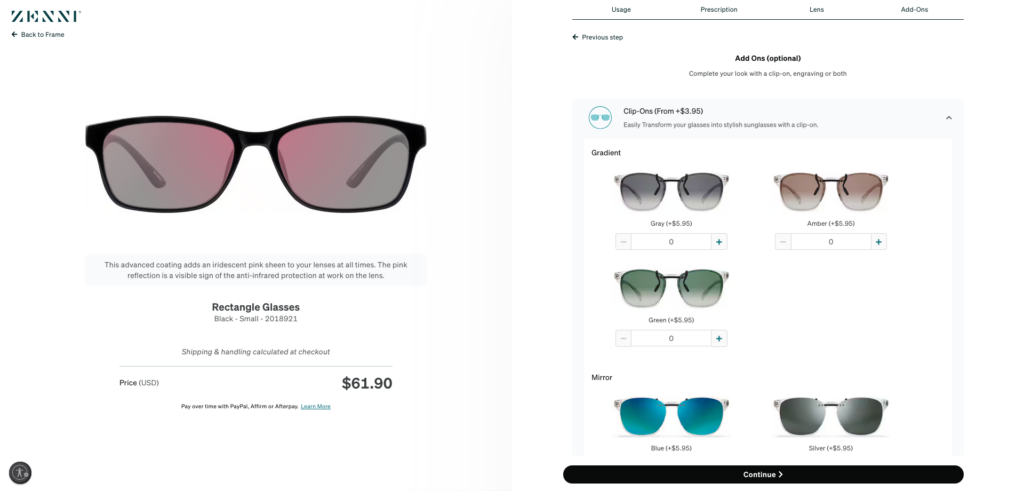
As mentioned, Zenni Optical’s glasses with Zenni ID Guard can block facial recognition based on near infrared / infrared light, including iris scanning. However, since all their lenses that can be coated with Zenni ID Guard are transparent for visible light, there can be cases where facial recognition systems based on visible light can get a good glimpse of the wearer’s eyes and identify the person. This is why, to block both facial recognition systems based on infrared light and those based on visible light, you can do the following: when you reach the ‘Add-Ons’ section of the lens selection process, you choose a clip-on pair of sunglasses (preferably with mirror tint), so that you can add the clip-on sunglasses over the infrared-blocking lenses and block both infrared light and visible light when you need it:
Since we mentioned ‘iris scanning’, it’s worth mentioning that ‘iris recognition’ is a highly accurate method of biometric identification that is very hard to deceive. Fortunately, in general, it requires the person to stand relatively still and look into the camera from a short distance, like under 1 meter. However, more advanced systems that use high-resolution cameras and near infrared light, assisted by complex software, are able to capture and read iris details from greater distances, up to 10 meters, even in the case of moving individuals. This is why, to block iris scanning it’s important to have a pair of glasses with lenses that can block near infrared / infrared light, like Zenni Optical’s glasses.
Therefore, standard facial recognition can be successfully obstructed by wearing the type of glasses described above, especially if the person also wears a wide-brimmed hat which covers most of the forehead and hides the eyes and forehead from overhead surveillance cameras.
Special attention must be given to a type of biometric identification referred to as gait recognition, which is the process of authenticating an individual based on their walking pattern. It captures the periodic micro-motions of the limbs, the posture, stride length, pace, etc. It can identify people at a distance, which makes it ideal for long distance, low-resolution settings. The problem is that you can’t easily change your fundamental walking pattern and covering your face doesn’t influence it. If we are to believe Huang Yongzhen (the CEO of a Chinese company that creates gait recognition systems), by using gait recognition, humans can be identified from up to 50 meters, with 94% accuracy, even with their back turned and even when they change the way they walk intentionally. So, gait recognition is presented as an absolute form of biometric identification that we can’t escape by any means. However, if we dig deeper, we find that the reality is quite different and the words from above are mostly Chinese commercial propaganda.
A 2023 study clearly lists the main limitations of gait recognition:
1. any variation in walking speed can change the gait pattern and lead to wrong identification.
2. footwear, clothing, or carrying objects (such as handbags, rucksacks, etc.), can alter the natural gait of a person and affect gait recognition.
3. unlike in laboratory conditions where in general cameras have a clear view of each subject at all times, in real life situations frequent occlusions that occur when other persons or different objects obstruct the view of the walking person, can substantially reduce the accuracy of gait recognition.
4. gait recognition is subject to spoofing attacks. Spoofing involves a person adopting an artificial gait pattern, to mimic the gait of another person. This study analyzes how the walking style of an individual can be mimicked by looking only at their photo.
5. environmental factors such as different lighting conditions, varying camera viewpoints, and different walking surfaces can greatly influence the accuracy of gait recognition.
6. other factors, such as age, health conditions and fatigue can also impact the accuracy of gait recognition.
A different study states that “the influence of clothing is generally unavoidable and has a considerable effect on the recognition rate.” It mentions that it was demonstrated that clothing can cause the recognition rate to drop from more than 95% to less than 33%. Another article specifies that “clothing variations can be seen as the most challenging factor for gait recognition”. Clothing variations refer to different clothing (like shirts, trousers, dresses, jackets, coats, etc.) worn by the same subject at different moments in time. It should also be noted that there may be significant differences between the clothing worn by the people used to train gait recognition algorithms and the clothing worn by real subjects who are analyzed using these algorithms.
At first glance it would seem that thermal cameras which convert thermal infrared radiation into visible light images, would render clothing irrelevant in terms of gait recognition, since they can ‘see’ through clothing. However, since in general, clothes are infused with body heat, it becomes challenging for thermal cameras to distinguish real silhouettes or fine-grained movements of legs and joints beneath clothing, especially in the case of loose clothing. With visible light-based cameras it’s also difficult to detect real body lines and limb movements beneath loose clothing.
Loose clothing masks the unique movements of limbs and joints, and alters the human silhouette, which is the main feature used by appearance-based gait recognition systems. This study specifies that “changes in appearance due to clothing variations, including coats, down jackets, baggy pants, and skirts, complicate the identification process”, while this article shows that “loose or restrictive clothing, for instance, can seriously influence a person’s movement, which in turn poses a problem as far as recognition is concerned” and it proposes the creation of new datasets that “should account for clothing variations, which significantly affect gait patterns. This includes different types of pants, shirts, and both heavy and loose clothing, all recorded in uncontrolled environments.” In spite of the claims of some studies that discuss skeleton-based methods that use depth sensors to map the skeleton, loose clothing poses a real challenge to gait recognition systems and can make person identification fail.
In conclusion, wearing loose clothing, that hide the real lines of the body and the unique movements of the limbs and joints, can make gait recognition fail, especially when it is coupled with other techniques like wearing special footwear or posture altering accessories, such as back braces.
This study shows that “gait pattern was demonstrably changed by footwear and was influenced by the kinematic constraint of the ankle joint and stiffness of the sole of the shoe.” Specifically, a type of shoes with thick, soft sole with rounded front and rear end, called ‘Stretch Walker’ or ‘Stretchwalker’ or ‘rocker sole’ shoes, were found to substantially change key characteristics of walking patterns which have an important influence on gait recognition accuracy.
These shoes are designed for maximum comfort and use stretchable materials to accommodate foot issues such as swelling. Their rocker-bottom sole provides comfort during long periods of walking. This article specifies that wearing the Stretch Walker shoes “changes the double support time, step width, and walking angle and increases step length and walking speed.”
Thus, to alter your gait and obstruct gait recognition systems, if you want to avoid the proverbial “pebble in the shoe” method, which may be effective but can cause irreversible damage to your feet, you can use the type of shoes described above, at least at those moments when you have special privacy concerns. Of course, if you want to use Stretch Walker shoes to conceal your true gait and deceive gait recognition systems, you will need to wear different shoes during your ‘ordinary walks’ as opposed to your ‘special walks’ when you feel your privacy is particularly threatened.
There are also the back braces created to correct posture, which is one of the key elements that affect walking patterns, with direct impact on gait recognition:
Since the majority of people tend to walk hunched over (slouch), wearing a back brace similar to the one from above can be a simple, discreet and affordable method of correcting your posture. By pulling the shoulders back, the back brace imposes a posture that is both healthy and aesthetic. It’s well known that changing posture has direct impact on the entire walking pattern: stride length, pace, head position and arm movement while walking, are all affected. Therefore, if you tend to slouch, wearing a back brace underneath clothing will change your gait to such an extent that it will most probably become unrecognizable to automatic gait recognition systems. Obviously, if you already have correct posture and you walk with a straight back, to disguise your gait you will need to remember to walk hunched over, which is always much easier than to walk with a straight back when you are used to walk hunched over.
It should be pointed out that apart from facial recognition and gait recognition there are also other types of biometric identification techniques used (or which can be used) in mass surveillance. Here is a list of them and of the corresponding countermeasures that you can take to neutralize them:
1. Ear recognition – is a biometric identification method that uses the unique shape, structure and 3D features of the human ear to indentify individuals. The ear remains relatively unchanged during life and has numerous characteristics that can be used to differentiate people. Fortunately, ears can be easily covered with many types of headphones, which will completely block ear recognition systems. Since it’s recommended to also wear a wide-brimmed hat to cover the upper part of the face, the best headphones / earphones for obstructing ear recognition systems are the “over-ear hook earphones” (often improperly called “clip-on earphones”), which cover most of the external ear, are very comfortable, while leaving the top of the head free to wear hats. They are comfortable because they don’t have a bridge between the two pieces that makes them press on the ears, like classic headphones:
2. Iris recognition – that was already mentioned, is a highly accurate biometric identification method that identifies individuals by analyzing the unique and complex patterns within the iris, which remain stable throughout a person’s lifetime. In general, iris recognition requires individuals to remain relatively still, at a short distance from the camera with near infrared illumination. Yet, modern systems manage to capture accurate images of the iris from larger distances, up to 10 meters, and even for moving individuals. Fortunately iris recognition can be prevented by wearing glasses with lenses that block near infrared / infrared (and visible) light, like the glasses described above.
Iris recognition should not be confused with another ocular-based biometric method called eye vein recognition (or “eye vein verification” or “scleral vein pattern recognition”), which is an authentication technology that scans the unique and intricate network of blood vessels in the sclera (the white part of the eye) using near infrared or visible light, to identify individuals. Although this technique has been explored and discussed in numerous articles, its implementation in the real world has been limited to mobile device authentication and banking apps, healthcare patient identification, banking services, like ATM transactions, and access to high-security areas in corporate or government buildings. Although in some cases this method can use simple and cheap hardware to capture eye images, like the front-facing camera of a regular smartphone, it can’t be used if the target person is at a distance larger than about one meter, if the person moves excessively or in poor lighting conditions. This is why it’s unlikely that it has been used in mass surveillance. However, to avoid the situation where your eye vein scans get leaked from a smartphone unlocking app or a banking app and end up in the wrong hands, it’s recommended to avoid using it with smartphones, as well as in real life (ATMs, hospitals, etc.), in those situations where it can be avoided. Otherwise, the person wearing the type of glasses described above, which block near infrared / infrared light (and visible light with clip-on sunglasses), can block eye vein recognition together with iris recognition, if these recognition systems get deployed in public places for mass surveillance purposes.
Another ocular-based biometric identification method called retina recognition (or “retinal scan”) identifies individuals using the complex and unique patterns of blood vessels on the retina (the thin tissue made up of neural cells, located in the posterior part of the eye). This method however involves casting a beam of infrared light into a person’s eye as they look through the scanner’s eyepiece, which makes it unsuitable for mass surveillance, so, it won’t be discussed in this article.
3. Palm recognition – is a contactless biometric technology that identifies individuals by analyzing the unique vein patterns and / or surface lines, ridges and creases of their palms. It is already used for access control (secure entry to buildings, offices, restricted areas, etc.), payment systems (Amazon One, Tencent PalmAI, etc.) and patient identification in healthcare. “Palm vein recognition” analyzes subcutaneous vascular patterns of the palm, which are unique and remain virtually unchanged throughout life. “Palm print recognition” analyzes the surface lines, ridges and creases of the palm. Multi-modal systems combine both techniques to achieve maximum accuracy. A near infrared light source is used to illuminate the hand, revealing the unique pattern of veins under the skin, or a high-resolution camera that captures the surface-level lines/creases/ridges of the palm. Researchers have even proposed systems that analyze the vein patterns of the dorsal hand, and combine the collected data with palm print and palm vein data to increase recognition accuracy.
Since all variations of palm recognition require the collaboration of the target individual, in the sense that the person who gets identified has to bring their hand at a distance of a few centimeters in front of the scanner, and since it has limited popularity, palm recognition is not really suitable for mass surveillance.
However, if it gains widespread use and millions of people integrate it in their everyday life, like for making payments, it may be easily used for mass surveillance. Even as it is now, the big problem that it raises is that in the event of a security breach where all the sensitive palm recognition data gets exposed and ends up in the wrong hands, you can’t change your palm vein pattern, like you change a password.
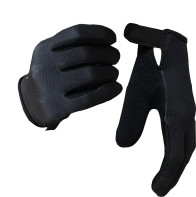
It’s recommended to avoid palm recognition systems whenever possible. While it may be more difficult to avoid them when they are used for access control in restricted areas at work or in hospitals that use them to identify patients, they are easy to avoid in other situations, such as when making payments for purchases. And in the event that future sophisticated palm recognition systems will be used to capture hight-resolution palm images of people walking on the streets, in stores, institutions, etc. wearing gloves will completely block palm recognition.
Gloves will also block the other types of biometric identification techniques involving the hands and fingers, like wrist vein recognition, hand geometry recognition, finger vein recognition and of course, fingerprint identification, if they are ever used without the individual’s consent, for mass surveillance.
4. Speaker recognition – is a biometric technique that identifies individuals by analyzing voice characteristics such as pitch, tone, accent, voice fluctuations when pronouncing specific sound sequences, etc., that differ between individuals. These patterns reflect both the speaker’s anatomy and learned behavioral characteristics.
It’s important to make the distinction between speaker recognition and speech recognition, which is a discipline that studies the methods and technologies used to transform spoken language into text or other similar data. So, speaker recognition focuses on determining who is speaking, while speech recognition is concerned with what is being said. The two are in general interconnected, since recognizing the speaker can simplify translating speech into text in systems that where trained on a specific person’s voice. However, they are different. To be noted that the term voice recognition is used to refer to both speaker recognition and speech recognition and this is why, to prevent any ambiguity, it’s advisable to avoid this term.
It’s a known fact that today millions of people use devices with “voice user interface” like mobile phones, cars, home automation or aircraft control systems, etc. They all use speech recognition. Automatic subtitling, automatic translation, hands-free computing (which is important for people with disabilities), interactive voice response (IVR) systems in telephony, access control systems with biometric scanners for multi-factor authentication, virtual assistants (like Apple’s Siri, Amazon’s Alexa, Google’s Google Assistant, Microsoft’s Copilot or Samsung’s Bixby), etc., all involve speech recognition, and many use speaker recognition processes.
Legit security and privacy concerns surround speaker recognition. Imagine what can happen if sensitive speaker recognition data falls into the hands of hackers as part of a security breach that can affect either the company that stores the data on their servers or the device that was used carelessly, without periodic software updates, etc.: voice-controlled devices can become accessible to unauthorized users, attackers can gain access to personal information such as address books, calendars, private messages, important documents etc. They may also impersonate the user whose data they possess and send messages or make online purchases on their behalf.
To avoid all these dangers it’s highly recommended to use speech/speaker recognition systems with great prudence, rejecting the services offered by tech giants like Google, Microsoft, Apple, Amazon, Meta, in favor of similar services offered by companies with a cleaner track record in terms of respecting users’ privacy. Also, it’s recommended to always choose locally installed apps and services over similar apps and services hosted in the ‘cloud’, or whose data gets transfered on the parent company’s servers.
There is also the common sense choice: instead of ordering pizza using Google Assistant and risking to have your voice characteristics uploaded and stored forever on Google’s servers, you can simply open the website of a pizza shop and order a pizza by pressing a few buttons. One thing is to use speech/speaker recognition to write a text using your voice when you have a temporary or permanent physical disability, and another thing is to blindly trust a tech giant like Google or Microsoft and entrust your voice profile to them when you search online information with your voice instead of typing the search terms, or when you unlock your phone with your voice instead of typing a pin, or for other trivial tasks that can be accomplished as easily by typing. Also, since speech/speaker recognition systems are frequently used in sectors such as healthcare, military, law enforcement, etc., it’s difficult to avoid them if you work in these fields and encounter them in the workplace. Yet, you can easily avoid them in your personal life where the convenience of sending commands to various devices with your voice has the downside of opening the door to dangerous privacy and security issues.
The bottom line is that speech/speaker recognition systems should be avoided as much as possible, especially when you know or suspect that behind them there are companies with zero respect for users’ privacy, like the well-known tech giants, when you know or suspect that the voice profile data is not stored locally but in the ‘cloud’ and when you have perfectly functional and convenient alternatives, like typing commands and search terms.
With speech and speaker recognition systems being so widespread today, it’s very likely that they have been used for mass surveillance and will be used for this purpose in the future, despite the promises made by the companies that create these systems. The antidote to mass surveillance carried out via speech/speaker recognition systems is to avoid using them as much as possible and to use better alternatives when interacting with electronic devices.
5. Keystroke dynamics recognition – identifies individuals using the specific rhythm and manner in which they type characters on a keyboard or keypad. The way an individual presses keys is used to create a biometric template of the person’s typing pattern, which can be used later for user authentication or identification. The time to seek and press a key (the “seek-time”), the time the key is held down (the “hold-time”), the time users take to get to specific letters on the keyboard, the speed of typing frequently used letters sequences, like “the” in English, are all taken into account.
Like gait recognition, keystroke dynamics recognition is part of a larger class of biometrics known as behavioral biometrics, in which the observed patterns are statistical in nature and consequently, they are less reliable than biometrics based on physically observable characteristics such as fingerprints or retinal scans. It’s well known that a user’s typing pattern varies significantly during the same day or between different days and can be affected by numerous factors such as fatigue, finger or hand injuries, etc. Therefore, no one should be intimidated by the claims of high recognition accuracy that can be found in various studies. Keystroke dynamics recognition is by no means an all-powerful biometrics identification method that nobody can avoid. One of the best ways to prevent keystroke dynamics recognition when using public computers in libraries and Internet cafés or touch screens in airports, hotels, restaurants, coffee shops, etc., where you don’t want to be recognized, is to type completely differently than you would normally type, like using only the thumbs from both hands, or only the small fingers from both hands.
6. Other rare, experimental types of recognition:
- body odor recognition – is a biometric technology that uses sensor arrays referred to as “electronic noses” (E-noses), that detect volatile organic compounds mainly emitted from the skin and breath, to identify individuals by their unique chemical signature. Although E-noses have been used in industrial applications to identify chemical compounds in vapors emitted by food products, packaging materials, petrochemical compounds, plastics, paper, etc., and it appears that this method has potential for non-intrusive identification of individuals, as well as health monitoring, disease detection, emotional state analysis, etc., body odor recognition remains an experimental biometrics identification method, with real limitations that substantially affect its accuracy rate. Odor stability is one of the main challenges for body odor recognition, as it is well known that body odor is greatly influenced by diet, stress levels, health issues, the use of products such as perfumes, deodorants, laundry detergents, etc. Changing environmental factors such as air temperature, air flow or different types of clothing, also have a significant impact on body odor stability. So, before starting to fear this immature and relative biometric identification technique, you should think at common sense countermeasures to defeat E-noses, in case they are ever used in mass surveillance: using strong deodorants and avoiding enclosed spaces with limited air flow whenever you suspect that ‘electronic noses’ might endanger your privacy.
- electrocardiogram (ECG), and electroencephalogram(EEG) signals have been proposed by researchers for person identification in niche applications, such as high-security access control systems, patient identity verification in healthcare, continuous authentication with various digital devices, etc. Standard electrocardiograms measure the electrical activity of the heart using electrodes placed on the subject’s limbs and chest, while electroencephalograms measure electrical brain activity using electrodes placed on the subject’s scalp. Although in recent years smartwatches or fitness bands have been successfully used to perform electrocardiograms, while various kinds or headsets or helmets have been used to perform electroencephalograms outside laboratory, collecting high-quality signals easily remains an important limitation. In addition, both ECG and EEG signals can change over time due to aging, stress, medication, various health conditions, etc. This lack of stability will degrade the accuracy rate of any biometric identification system based on ECG or EEG signals, if such systems are ever used in real life. Since having your ECG or EEG signals collected involves voluntary collaboration and physical contact with the measuring instruments, it’s unlikely that ECG and EEG signals will be used for mass surveillance in the foreseeable future. However, using smartwatches, fitness bands, headsets, helmets or other wearable devies with multiple functionalities which include ECG and EEG signal recording, can lead to serious sensitive personal data exposure, especially when these devices send your data over the Internet to remote servers for processing. Therefore, the best countermeasure against mass surveillance carried out through ECG and EEG signal analysis, if these methods are ever used in real life for mass surveillance, is to avoid using wearable devices that record ECG or EEG signals, especially if you know or suspect that they transmit ECG and EEG data to third parties.
- lasers detecting heartbeat through the throat have also been proposed. This technique involves shining a laser beam on to the skin of a person’s throat and using a high-speed camera which can record images at speeds of 2,000 frames per second, to capture light reflections in order to measure exactly how much the skin is rising and falling as the main artery expands and contracts during heartbeats. Complex algorithms are then used to filter out all other movements, such as chest movements caused by breathing, except the minute vibrations caused by the person’s heartbeat which are on the scale of a few billionths of a meter. In short, this technique could have various applications in healthcare, where it may be used instead of stethoscopes to monitor patients’ heartbeat, but we shouldn’t worry about it as far as mass surveillance is concerned. To capture an individual’s heartbeat and use it as a means of biometric identification, this method involves shining a laser beam on to a specific spot at the base of the throat, while the person ramains relatively still at a specifc distance. To expect this method to be used in public places to identify individuals without their consent would be, at least in the current situation, an exaggeration. If this technology is ever integrated in devices used in domestic settings, the best way to prevent the privacy issues that they can create is to avoid using those devices, especially if you know or suspect that they send biometric data over the Internet to remote servers for processing.
- microbiome analysis – is a forensic identification method that uses microbial organisms such as bacteria, fungi and viruses that live on and in the human body, especially on the skin, to identify individuals. Since people constantly shed these microorganisms onto the surfaces they touch, this method allows linking individuals to objects, locations or victims, even when DNA or fingerprint evidence is unavailable or degraded. As its description suggests, this method is only used in forensics and even there only as an auxiliary tool intended to supplement the traditional techniques of DNA and fingerprint identification, being well-known that a person’s microbiome changes over time and can be substantially influenced by diet, health issues and environmental factors such as air humidity and that space sharing, such as with cohabitating couples, can cause microbiomes to become similar, reducing identification accuracy. So, for the time being, you shouldn’t worry about microbiome analysis as far as mass surveillance is concerned. Even if this method is ever used in mass surveillance, you can always use gloves when touching objects in public places, to stop transferring your microbiome to objects.
- polarimetric thermal imaging – is an imaging technique that measures both the intensity and polarization of the light emitted or reflected by human skin. Different variations of this technique provide highly detailed images of the skin surface as well as geometric data that conventional thermal or optical cameras cannot capture. Human skin naturally emits long-wave infrared radiation (8-14μm) and infrared light can be also projected onto the skin from various angles. Unlike conventional thermal cameras that only record radiation intentisy, polarimetric thermal imaging cameras capture polarization states of the emitted or reflected light, which is sensitive to surface shape and texture. This makes it suitable for use in 3D facial recognition systems, especially in low-light or nighttime conditions. It can be also used in dermatology, for latent fingerprint acquisition and for improving iris recognition.
We already discussed facial recognition, thermal cameras, iris recognition and fingerprints. First of all, don’t be intimidated by the precious terms used to describe this technique or other techniques in various studies and articles. Polarimetric thermal imaging is nothing else but a technique that is supposed to enhance individual recognition rate in 3D facial or iris recognition systems, which will remain forever imperfect and limited, in spite of using this “add-on”. If you consider some of the limitations of this technique, such as image quality issues, high sensitivity to noise, complex radiometric calibration requirements, ambiguity in data interpretation regarding the true polarization state of light, influence of environmental factors such as rain, fog, smoke etc., you will understand that polarimetric thermal imaging is much weaker and less accurate than it seems at first glance.
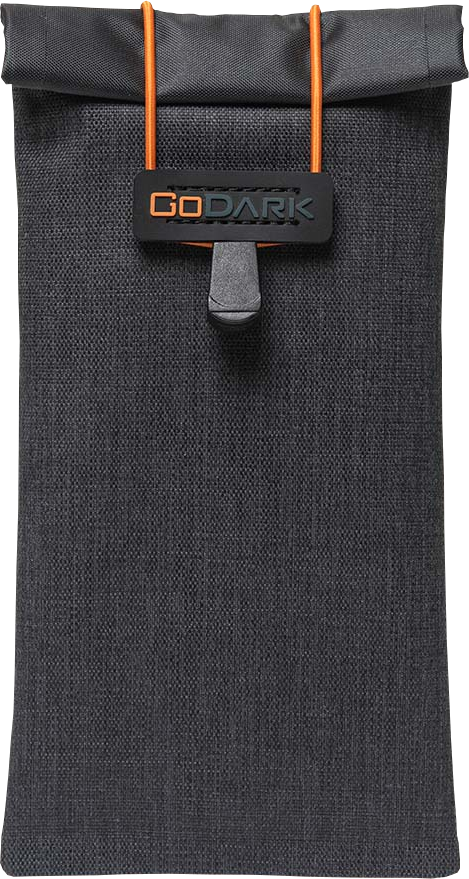
The second arm of mass surveillance is mobile phone tracking. Fortunately, mobile phone tracking is much easier to avoid than person recognition via surveillance cameras. It all comes down to enclosing mobile phones in Faraday bags.
Faraday bags are bags lined with conductive materials like copper, that create Faraday cages around the enclosed objects, blocking incoming and outgoing electromagnetic signals. (A Faraday cage is a mesh of conductive materials which block electrical fields by causing the material of the cage to distribute its electric charges in a way that cancels out the field’s effect inside the cage.)
Thus, Faraday bags can block all incoming and outgoing mobile (4G/5G), Wi-Fi, Bluetooth, GPS, RFID (Radio-frequency identification), and NFC (Near-field communication) signals. It can also protect against electromagnetic pulses (EMPs), which are short bursts of electromagnetic energy that can damage electronic devices and power grids. They can be created by nuclear and non-nuclear explosions or natural events like solar storms. En EMP induces high currents in wiring and electronic circuits, causing thermal damage.
Faraday bags, which can take the form of a small pouch, a sleeve, a waist belt, a small handheld bag, a Duffel bag, a large bag for full tower computers, etc., have three main uses:
- they protect phones, laptops and other digital devices from tracking, unauthorized access and electromagnetic pulses.
- they prevent car theft by blocking the signal from key fobs, preventing thieves from using boosters to unlock or start cars.
- in forensics they are used by law enforcement to prevent remote wiping of devices they seize.
At first glance, mobile phone tracking could be stopped without putting the phone in a Faraday bag, by turning off the phone. Even if that were true, you would still have to turn on your phone and then wait a long time before you could use it again to make calls, send messages, use the camera, etc. But it’s not true.
One of the subsystems that make up a modern mobile phone, often referred to as the “baseband”, has its own dedicated processor, RAM and flash memory, runs its own dedicated operating system, allowing it to function independently from the phone’s main processor and operating system. It controls and operates the radio transmitter and receiver, managing the wireless radio functions and communication with the cellular network. This means that the phone can appear to be “turned off” while the radio subsystem remains powered and operational.
When you turn a mobile phone off, it can enter a low-power state, in which it has full receiving and transmitting capability. The screen will be turned off, so, it would provide the false impression that the phone is completely turned off and you are safe from tracking. Apple’s “Find My” app is a proof of this behavior.
A message displayed when an iPhone is turned off specifies: “Find My helps you locate this iPhone when it is lost or stolen, even when it is in power reserve mode or when powered off.”
As electronic devices become more complex, it becomes more and more difficult to know how our phones, tablets, laptops, smartwatches, etc. operate and what programs or functions are in an ‘always-on’ state.
It’s important to note that airplane mode doesn’t help either. Setting a phone to airplane mode only prevents the device from transmitting, but it still receives signals. The phone still records data like location history, to transmit it later when the phone reconnects. A Faraday bag prevents this issue by blocking incoming GPS and cell signals used by mobile phones to record location. Since this stops phones from recording, they will have nothing to transmit later.
The same is true for laptops. If a laptop is in sleep or hibernation mode it’s not fully powered off and some systems, such as the RAM are still active and vulnerable to data theft via Wi-Fi, if the operating system is infected with malware. Even if the laptop is powered off, it can have features that allow it to remain partially active, like the wake-on-LAN function, which allows the laptop to be turned on remotely, or quick start-up features that enable a faster boot up. As long as some subsystems are active there is always a certain risk of remote hacking and tracking.
Tablets, smartwatches and other similar devices are also vulnerable to tracking even when powered off or in airplane mode.
This is why enclosing a digital device in a Faraday bag for short periods of special privacy concerns or when travelling is the most effective way of preventing remote tracking and hacking while also protecting them from EMPs.
So, mobile phone tracking can be prevented by using Faraday bags like this:
Laptops can be protected against data theft and tracking using Faraday bags for laptops:
Multiple digital devices can be carried in handheld Faraday utility bags:
Chip-enabled credit cards, IDs and passports, which use RFID signals to transmit data, can be also protected using waist belts:
There are wallets that can hold cash while protecting cards and IDs from RFID skimming attacks using metal lined pockets and panels. You can also flip open these wallets and slide your phone into the faraday cage pocket, to cut off all cell, Bluetooth, GPS, and Wifi signals:
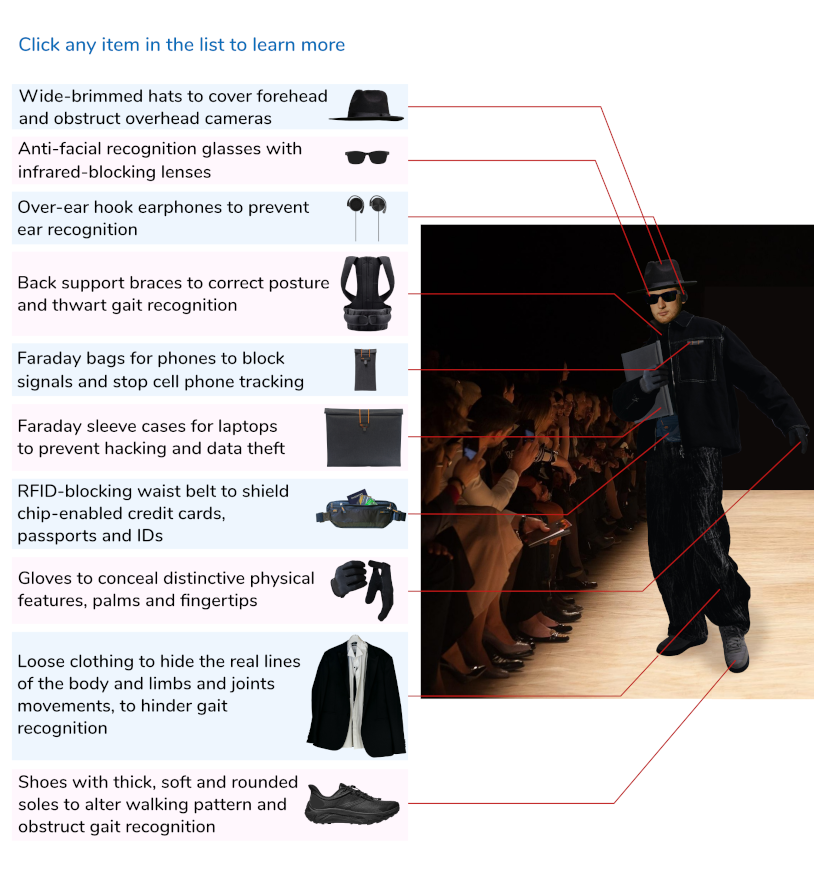
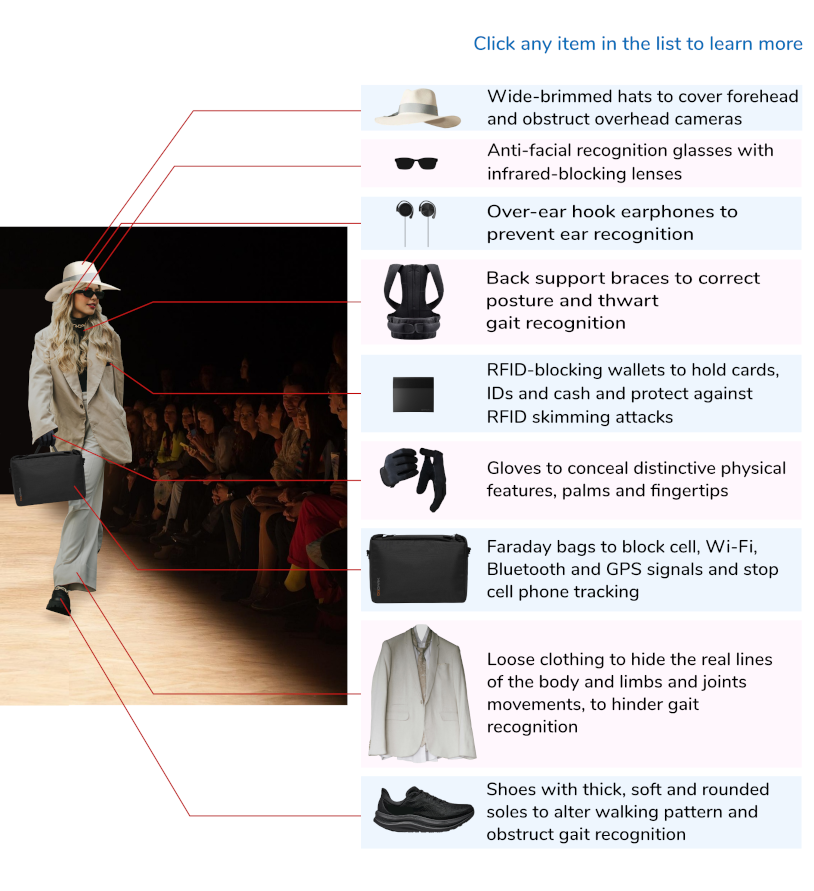
Therefore, journalists, activists, business travelers and anyone who wants to maintain their privacy and protect their data for short periods of intense privacy concerns, can wear the products listed below. The complete outfit of privacy-minded individuals in this digital age is conceived as a veritable “privacy armor” that prevents cell phone tracking and obstructs facial / iris / ear / palm / gait recognition by surveillance cameras, while remaining discreet, elegant and blending in easily in almost any social environment:
Other proposed methods to obstruct facial recognition, such as extravagant makeup, face masks, scarves or shirts or dresses with various patterns, thermally reflective hoodies, fancy eyeglasses or hats with rows of infrared LEDs, fake beards or moustaches or wigs, are not only less effective, but are not practical, attracting attention, making it impossible to blend in. You can also imagine the embarassing situation you may face if you meet a close friend while wearing some computer vision dazzle makeup.
The idea that you shouldn’t try to avoid mass surveillance because it’s too widespread and uses technologies that are too advanced to be defeated, doesn’t hold water either. The numerous false positives or false negatives that all human recognition systems frequently generate, and the limitations of signal transmission and reception in mobile telephony, prove that mass surveillance is by no means a well-oiled machine that sees all and knows all, like you see in spy movies. Instead of playing the victim and giving up, we should fight against mass surveillance both actively and passively, always being prepared to confront the latest technologies and techniques used against us. Privacy shouldn’t be a luxury. Privacy is a precondition of freedom and a non-negociable right of every citizen. The state and private corporations should know when they have crossed the line and should keep their distance.
The links to some physical products in this article are affiliate links, which means that if you follow one of these links and purchase a product, we receive a small commission, while you pay the same price as when you visit the product’s website directly.